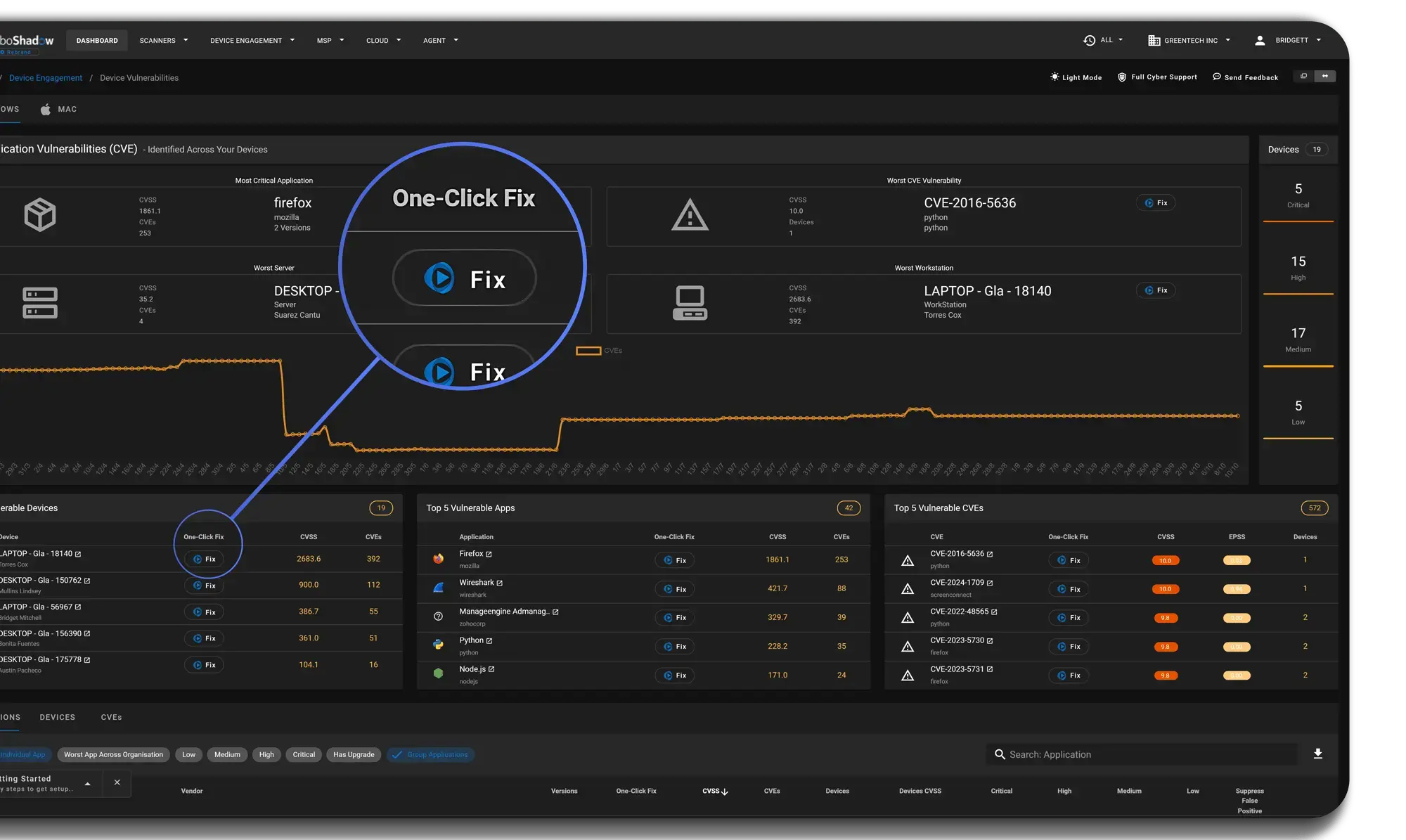
Cyber Heal 'AutoFix'
Remove 80% of Remediation via Automation
Using our Cyber Heal technology, our AutoFix process remediates issues across the estate automatically whilst updating your PSA / Help Desk System .- Update over 7000+ Applications from Microsoft Winget Repository.
- Rapidly uninstall unwanted or unsecure applications.
- Manually update less popular titles using your own MSIs / EXEs.
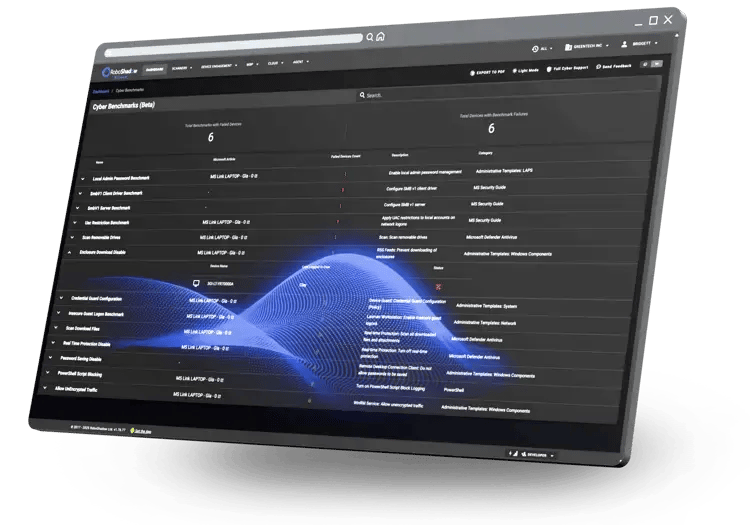
- Change Cyber Benchmark configuration to meet compliance standards.
- Update Firewall and Anti-Ransomware settings.
- Automate all the Cyber Heal tasks in the background with AutoFix
- Log any AutoPilot fails into your Service Desk System / PSA for a follow-up.
No Vulnerability Left Behind.
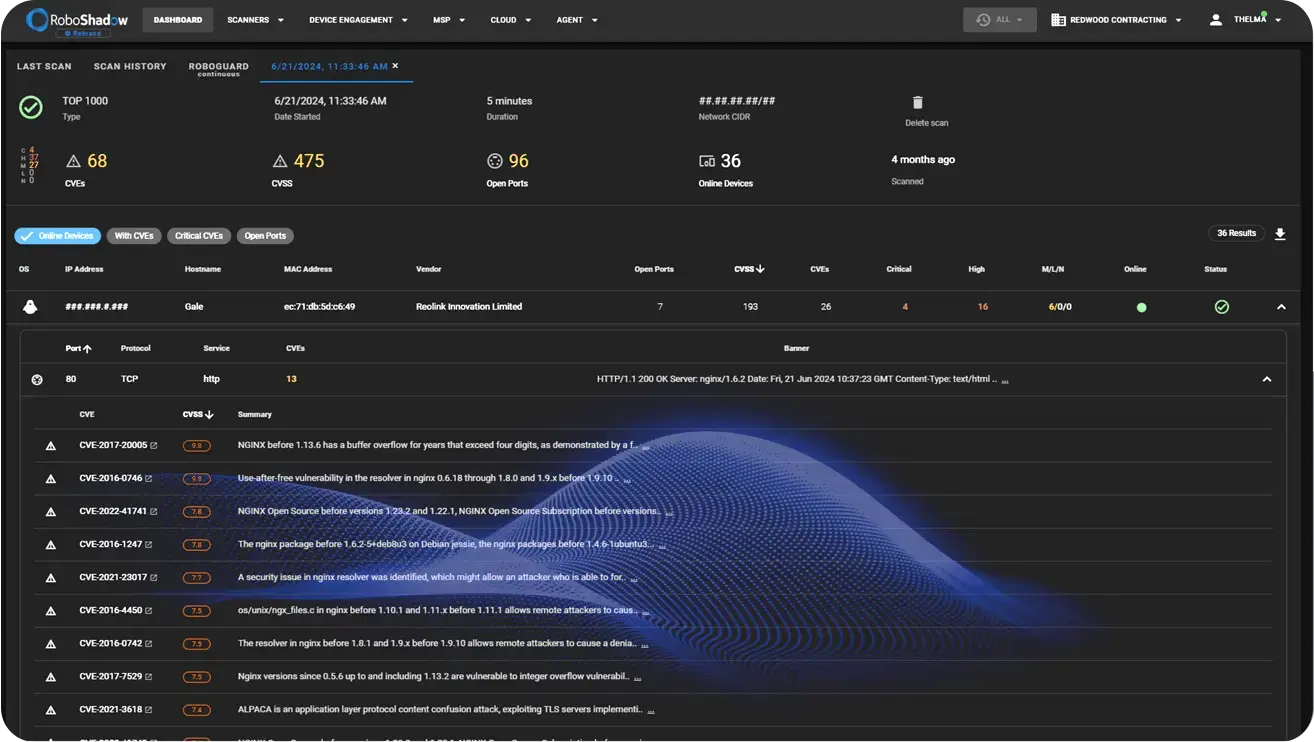
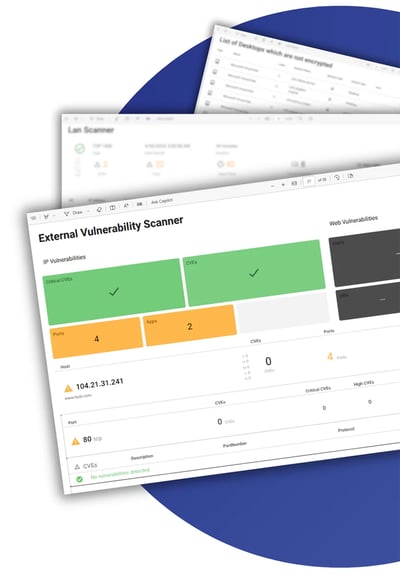
in our External 'Attack Surface' Scanner

Simply enter your IP Addresses & Websites, and access a dashboard that gives you a detailed report of vulnerable ports, IPs, CVEs, and Website Vulnerabilities. From this dashboard, you can easily monitor and prioritise your top vulnerabilities so you know what needs immediate attention.
Our system automatically scans and sends results directly to your email every day.
%20HD%20png-1.webp)
Find the weak link.
LAN scanner
The RoboShadow LAN Scanner performs a device discovery scan on your local network, followed by a full vulnerability assessment across the whole network subnet.
The LAN Scanner shows you what devices internally are vulnerable and reveals where the bad guys could hide if they get in. The scanner helps you understand and manage your internal attack surface and covers the following scenarios:
- What vulnerable IoT devices could a hacker hide in?
- Are your networks open (flat), or are they properly segregated?
- Which network equipment has exploitable vulnerabilities?

LAN Scanner
%20(2).png?width=500&height=83&name=Add%20a%20heading%20(5000%20x%204322%20px)%20(2).png)
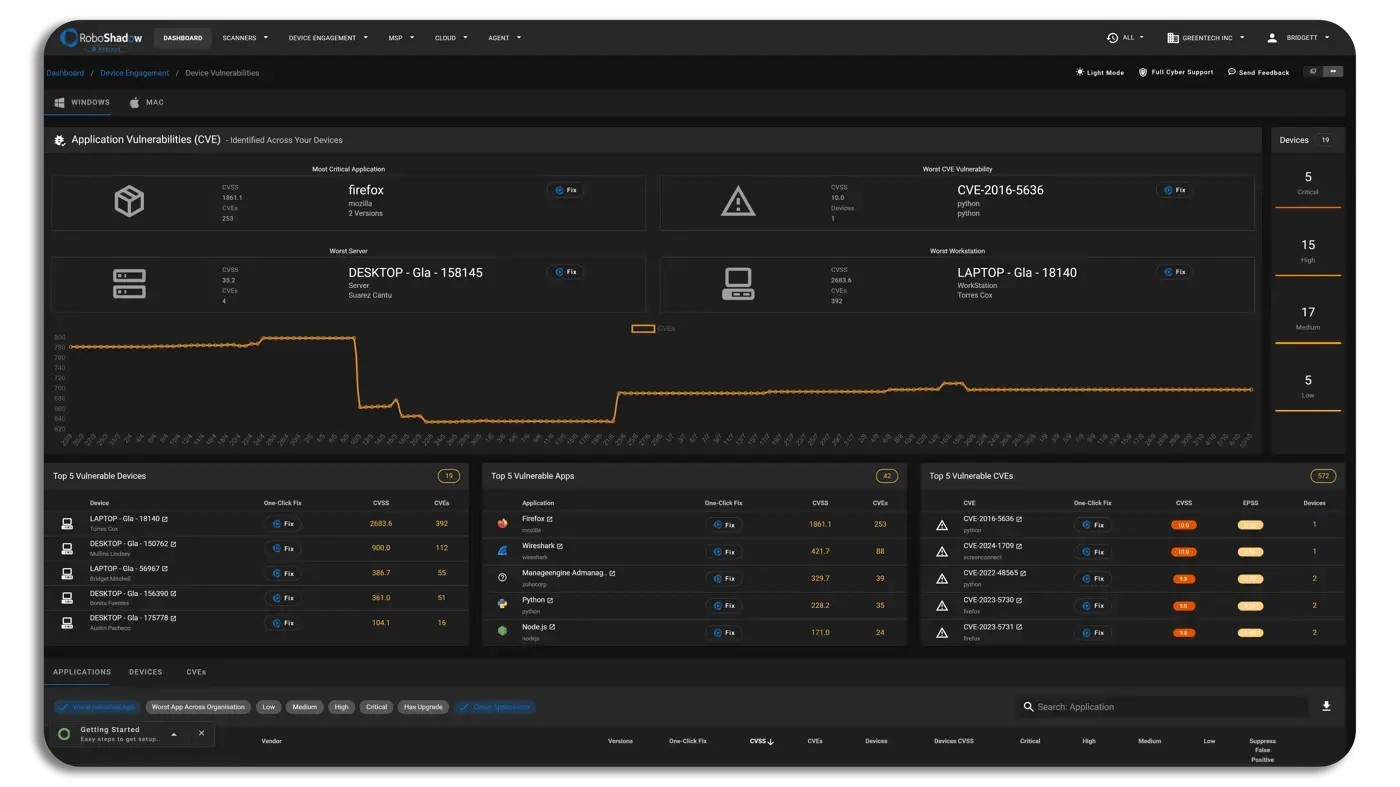
Device Vulnerabilities

Anti-Virus

OS Updates

Device Encryption
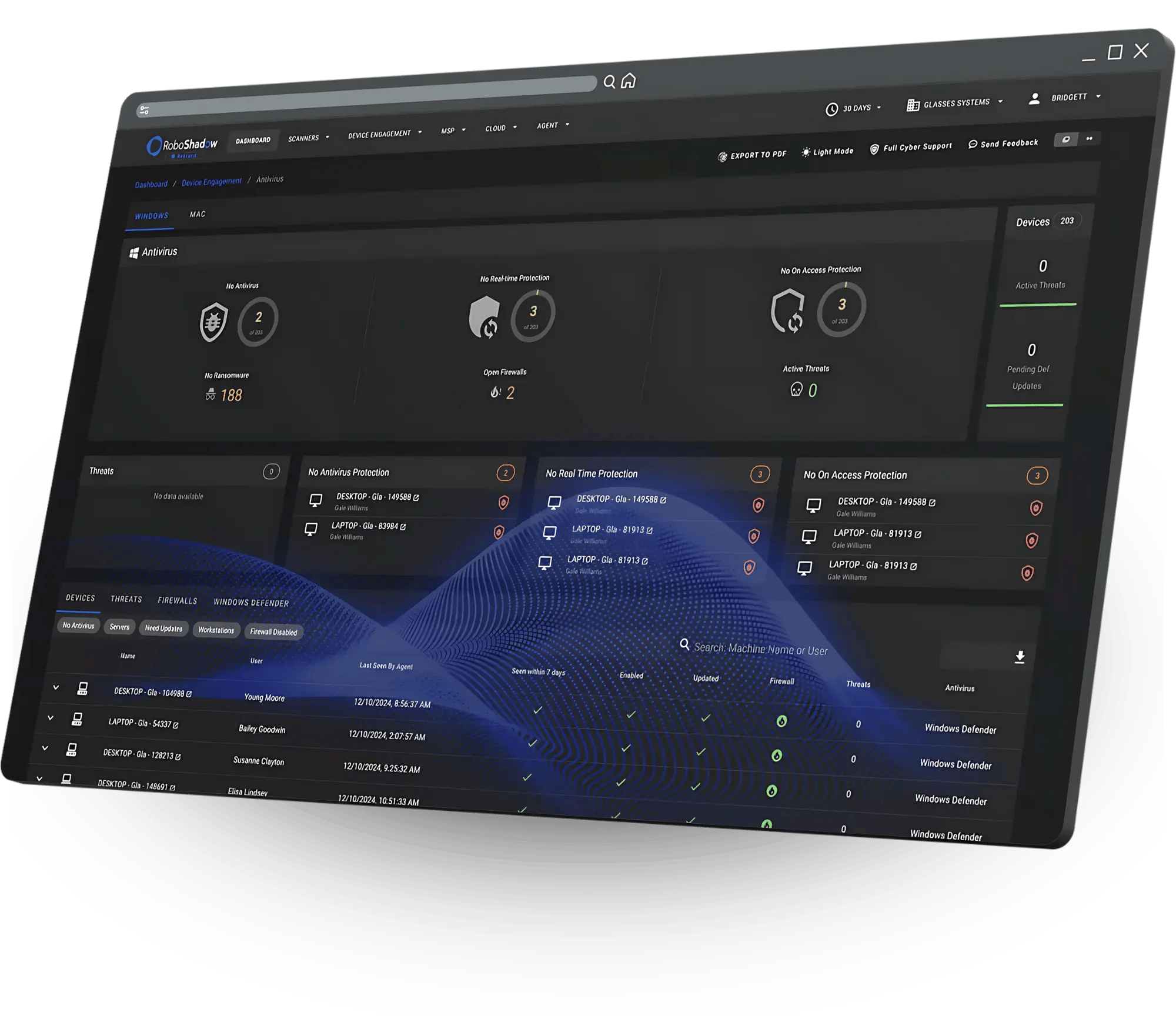
every Anti-Virus on the planet .
Anti-Virus
RoboShadow integrates with just about every AV on the planet and allows you to centrally manage the core fundamentals to check if it’s turned on, and if it’s updated etc.
RoboShadow integrates with Zendesk, Jira, Windows Defender, Malwarebytes, CrowdStrike, ServiceNow and more!
.png?width=378&height=71&name=_Final%20Brochure%20(13).png)
The Microsoft Essentials Security Hub.
Sync with Defender , Intune & 365
Easily link data from Microsoft 365, Intune, and Windows Defender into RoboShadow. Pull in MFA authentication, Intune device insights, and track Defender vulnerabilities. You can even roll out RoboShadow to your whole estate using 1-click via Intune.

.webp)
Cyber
Community
Our Free Tier is named as "Worlds best Cyber Free Tier" as 90% of our product is included. We provide you with the tools to be able to successfully manage and enhance your security.
£0
- External IP Attack Surface Scan
- Website Security Scanner (OWASP)
- Windows CVE Reporting
- Integrate fully with 365
Cyber
Professional
All Community features plus AI tech, continuous scanning, 1-click fixes, Shodan integration, attack mapping, and priority scans. £20/month , £1 per agent
£20 / mo + £1 per agent
- Cyber Heal ‘AutoFix' (£1 per agent)
- RoboGuard Vulnerability Alerting'
- PSA & Ticket Integration
- Realtime Agent Reporting
Cyber
Enterprise
Includes all features of 'Cyber Professional' plus an advanced governance team layer, specifically designed for higher-level teams requiring enhanced oversight and management capabilities.
£200 / mo
- Account Manager
- Cyber Governance Support
- Yearly Penetration Test Support
Seamless PSA Ticketing Integrations
for Total Cybersecurity Control.
RoboShadow integrates with Zendesk, Jira, Windows Defender, Malwarebytes, CrowdStrike, ServiceNow and more!

Continuous Cyber Scanning
Continuously Scan your attack surface every day and get alerts with any new vulnerabilities.
Meet your obligations for various Cyber Frameworks to demonstrate you perform continuous vulnerability scanning across your entire estate.
.webp)
'Stand Alone' Tools Within The Platform.
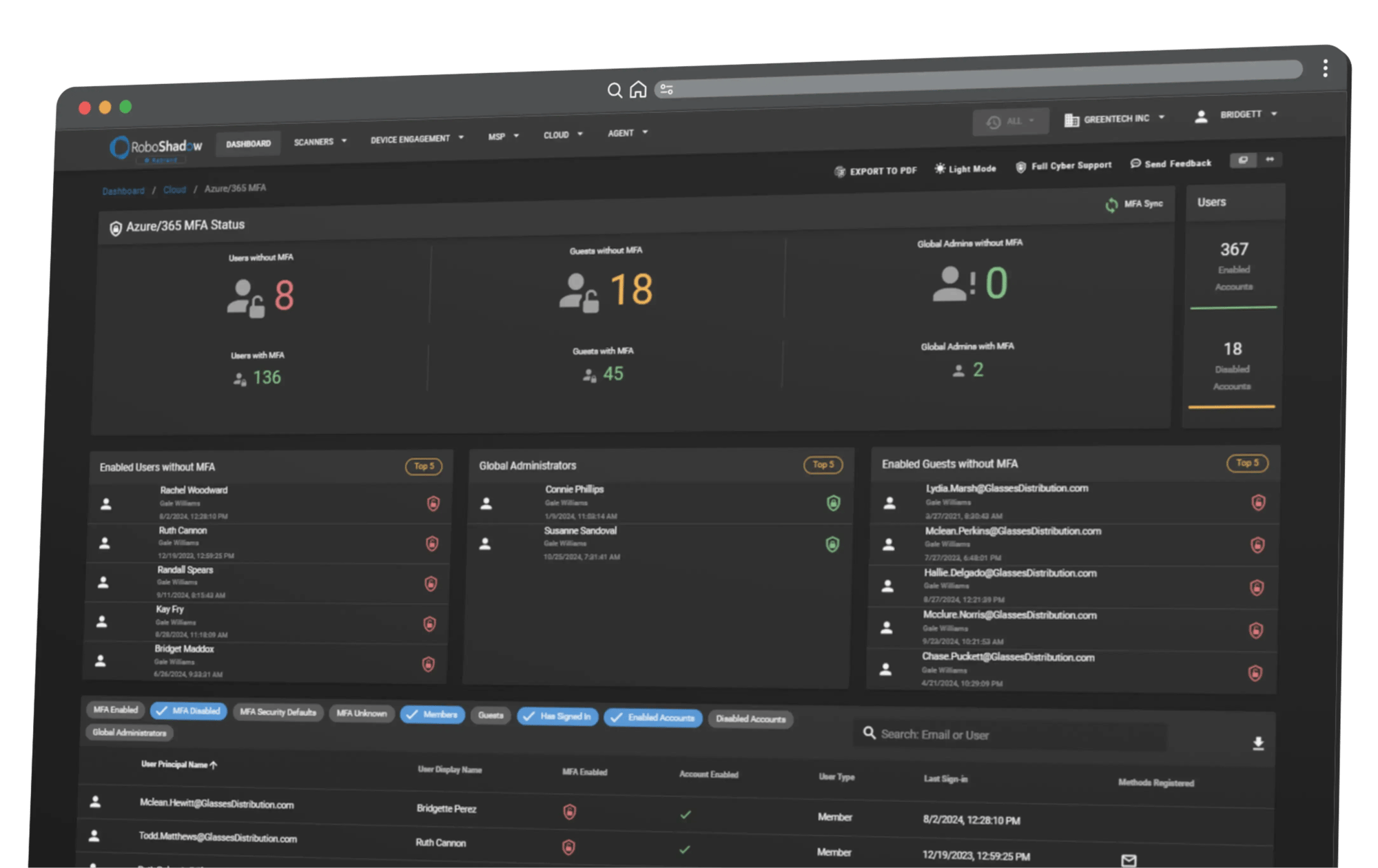
MFA
MFA is the "lowest hanging fruit to attack.” That's why robust MFA Auditing is crucial.Our MFA Non-Conformance Report tracks compliance, including:
❍ Guest User MFA Reporting
❍ Global Admins Compliance
❍ Update Reboot Reporting
❍ Azure AD Reconciliation
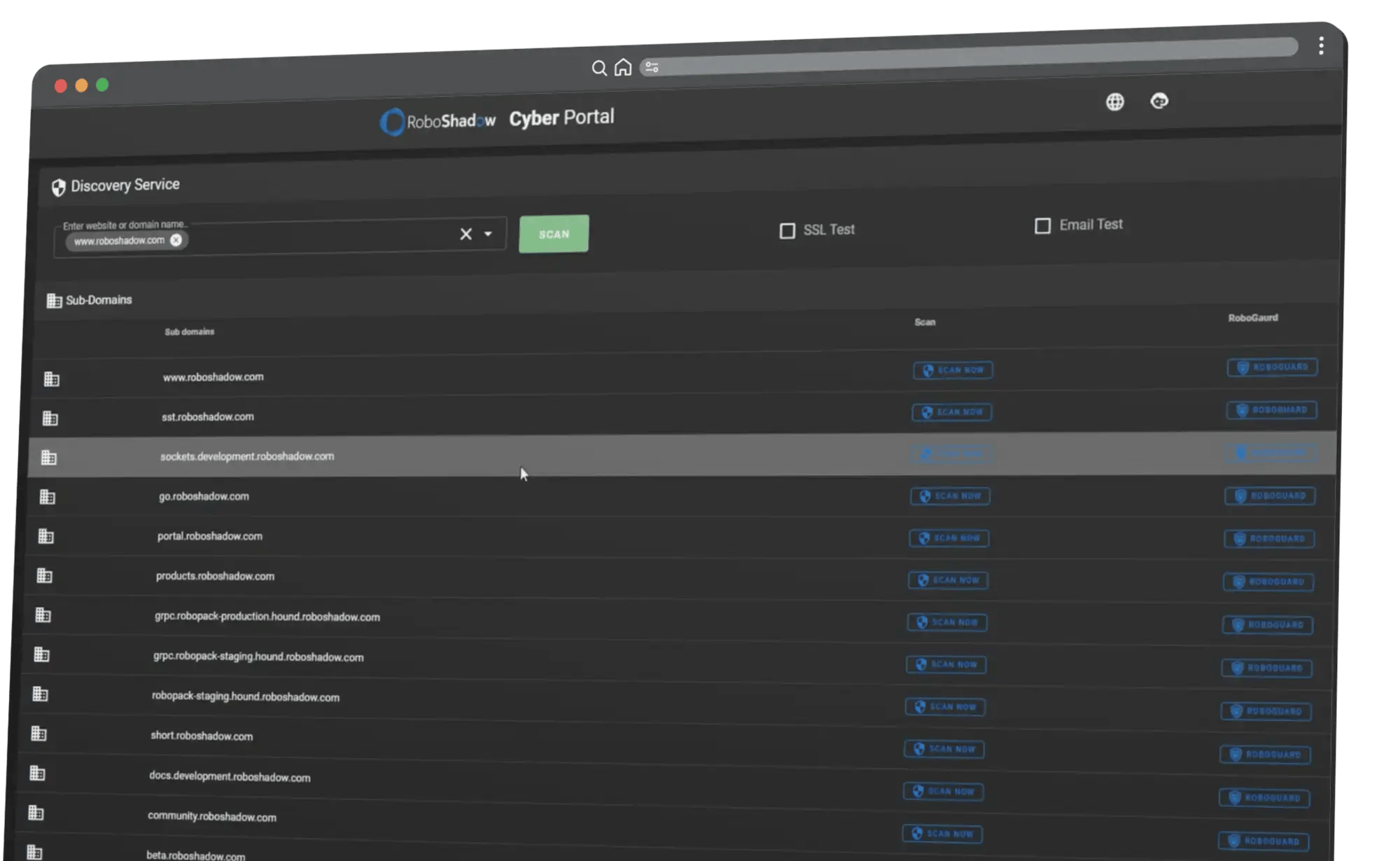
Domain Enumeration
The Domain Enumeration feature allows users to quickly identify all subdomains and backend systems associated with their main business domain, highlighting potential security risks.
By scanning these often-overlooked areas, users can gain insights into assets that may be vulnerable to attack, such as test environments and staging servers. This free tool in RoboShadow’s platform empowers businesses to secure their digital infrastructure more effectively and proactively.
As Seen On YouTube
like. Comment. Subscribe.
@RoboShadow • 2.91k Subscribers • 51 videos
Through YouTube, we can connect with our community and provide in-depth tutorials on getting the most out of RoboShadow. If you have any questions or suggestions for video content, feel free to reach out to us at Hello@roboshadow.com.
What Our Clients Say...
-
"Many more clients are being asked by their clients and insurance companies for evidence that they are conducting regular vulnerability scanning, and RoboShadow makes it super easy to run scans on our client networks, resolve issues, and produce lovely-looking reports for our clients."
.png?width=50&height=50&name=Untitled%20design%20(34).png)
Aaron Nihat
-
"RoboShadow is super quick to setup and cost effective Cyber management."

Manny, 3GV
-
"The RoboShadow platform allows us to keep tabs on our External Attack Surface."

Ben, Crank
-
"An essential security and analysis tool… I use it every day!"

Bernie, Ultumus
-
"The Robo Shadow platform worked wonders for our Penetration Testing."

Kevin, Hotwire
-
"Responsive, friendly and cost-effective security solutions. I'd happily recommend them to industry peers."

David
Around the world, we all have different ways of proving our Cyber Security posture. For many businesses, using a good governance framework is a great way of proving to your customers, regulators, and investors how seriously you take your cyber governance.
RoboShadow has a compliance engine built within the platform, allowing you to export evidence data for a whole host of cyber governance frameworks including but not limited to:
• Cyber Essentials (UK)• Essential 8 (Australia)
• NIST (US)
• SOC 2 (Worldwide)
• ISO 27001 (Worldwide)
• HIPAA (US)




-png-1.png?width=70&height=70&name=MicrosoftTeams-image%20(53)-png-1.png)
