5 Essential Strategies for Cyber Governance (for MSPs & SMBs)
Every organisation has some kind of cyber risk. It’s just the reality of using technology to run a modern business, whether you’re an MSP managing dozens of client estates or an SMB running your own infrastructure.
In case you're feeling alone in this, it's worth noting that the Cyber Security Breaches Survey 2025 found that 43% of businesses and 30% of charities reported experiencing a cyber security breach or attack in the last 12 months - so it really isn't uncommon.
The challenge is how that risk is communicated, documented and governed, especially when you’re accountable to regulators, customers, investors, and even internal staff. Governance matters because cyber security today isn't judged purely on whether an incident happens, but whether an organisation understands its exposure, prioritises it properly, and documents how those decisions were made.
In a YouTube video we posted a little while back, Terry walks through what he sees organisations often get wrong about cyber governance, and how to approach it in a way that is practical, defensible and commercially sensible.
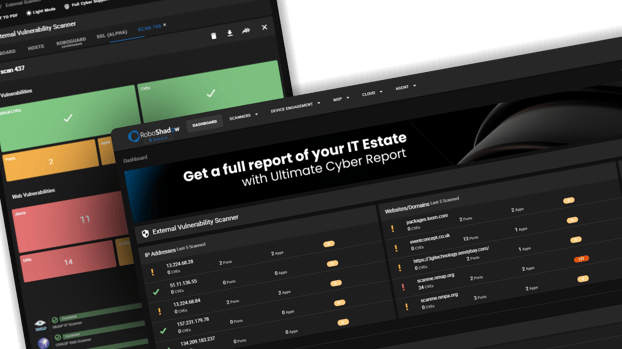
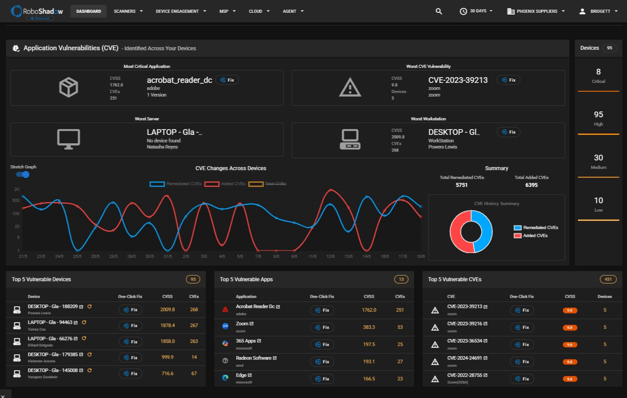
RoboShadow aims to help customers manage internal governance with investors, regulators, internal staff, customers, and clients.
There’s no magic toolset involved. In many cases, it really can just be a structured spreadsheet and a disciplined process. However, there are some fundamentals that MSPs and SMBs quite often get wrong. A big part of our mission is to ‘demystify’ and simplify cyber security, so here’s a readable guide of our top 5 Essential Strategies for Cyber Governance.
1. Stop Treating Cyber Risk as Something to Be Ashamed Of
One of the biggest governance mistakes is cultural. There’s sometimes an assumption that having cyber risk means you’ve failed or that it’s something to hide or minimise.
But logically, if you’re using cloud devices, running websites, storing customer data, or giving people laptops, you are exposed to risk.
“Cybersecurity risk is not something organizations should be ashamed of. Nearly every organization has some form of cyber risk.” - Terry Lewis, CEO, RoboShadow.
This reframing is very important, because when risk is treated as embarrassment, it gets buried. If it gets buried, it isn’t logged - and if it isn’t logged, it can’t be governed.
Good governance starts with accepting that risk exists as a normal by-product of doing business. The end goal is to understand risk, prioritise it and manage it transparently; you won't completely eliminate it. Regulators and stakeholders prefer your honesty, paired with a clear plan.
Ultimately, cyber risk simply needs to be understood, recorded and managed, just like any other business risk.

2. Cyber Risk Is Not Just 'IT’s Problem'
Another common fallacy is that cyber risk belongs solely to the IT or operations departments.
The difficulty with this mindset is that cyber security risk is closely tied to money and business priorities. Decisions about whether to invest £50,000 in remediating a particular platform, or whether to accelerate a migration, are not purely technical choices. They are risk-vs-cost decisions. These budget decisions are made by leadership, therefore, cyber risk must sit at leadership level.
Despite this, only around a quarter of businesses said a board member had explicit cyber responsibility last year (source). If no one at the top owns the trade-offs, it can be easier for cyber risk to drift into that 'IT's problem' mindset by default.
“Quite often, the people who distribute the money in an organisation like to point fingers and say, ‘We didn’t know we had this risk.’” - Terry Lewis, CEO, RoboShadow.
This is one of the reasons standards like ISO 27001, SOC 2, and Cyber Essentials exist. They’re there to ensure that the people who make financial decisions have visibility of the risks attached to those decisions.
MSPs should take particular note here. IT might surface the problem and propose solutions, but the responsibility for accepting, mitigating, or funding a risk sits squarely with leadership. If you’re managing infrastructure on behalf of clients but not ensuring risk is escalated to the right decision-makers, you’re leaving yourself exposed. Your job is not only to remediate vulnerabilities, but also to make sure risk is properly understood at board level.
3. Ignorance Is Not a Defence
There’s a persistent belief in some organisations that if you don’t explicitly acknowledge a risk, you won’t be held accountable for it later; this approach rarely (if ever) survives regulatory scrutiny.
“If you have an incident and you’re having to face customers and regulators pretending you didn’t have that risk in the first place - that’s when you really get into trouble.” - Terry Lewis, CEO, RoboShadow.
Ignorance is what creates liability, and raises questions like:
- Why were there no risk assessments?
- Why were there no vulnerability scans?
- Why wasn’t there even a basic log of known issues?
In October 2025, the ICO fined Capita £14m for failing to ensure personal data security in relation to a 2023 cyber attack. In its summary of contraventions, it points to issues that are very much governance‑shaped: failure to prevent privilege escalation and lateral movement (flagged multiple times but not remedied), slow response to a high priority alert, and inadequate penetration testing and risk assessment.
We're not saying this to scare you, we just want to double down on the concept that regulators and customers aren’t looking for perfection, but they do expect responsibility. The risk of ignorance isn't worth it.
The UK regulator is pretty open that documentation exists so that you can demonstrate what you're doing and why, and you may need to produce it during an investigation (source). So if a vulnerability was identified, logged and accompanied by a management plan, the organisation can demonstrate it acted as a “good citizen”. Even if an incident occurs, the presence of documented governance could reduce the likelihood of individual culpability. So overall, governance is about being able to evidence your thinking.
4. Prioritise Risk by Understanding Criticality
Not every vulnerability represents an existential threat, so not every remediation needs to happen immediately, and not every budget cycle allows for instant correction of every issue.
Risk management is particularly relevant when costs are non-trivial; remediating a platform could require a budget that may not exist mid-cycle. Terry uses a straightforward example: if a public-facing website is compromised but holds no critical business data, its remediation plan may reasonably align with the next development cycle rather than triggering emergency spend. You can demonstrate this quite easily in a simple spreadsheet (see number 5).
“Don’t think that every single piece of risk has to be solved now otherwise everyone’s all going to be going to prison on cyber security charges, it just doesn’t work like that.” - Terry Lewis, CEO, RoboShadow.
We'll give you another example to support this: the 2025 DBIR executive summary says that though organisations worked very hard on patching, only about 54% of edge device vulnerabilities were fully remediated throughout the year, and that it took a median of 32 days to accomplish.
Governance requires balance, and RoboShadow can give you that, making sure you can demonstrate good vulnerability assessment processes, ensuring that each risk is being looked at on a business and data protection level, and that you have management capabilities in place.
5. Log It Properly, and Escalate It
There isn’t a complex governance platform required to start on this. In fact, the ICO explicitly says that documentation can be kept in "many different ways", from basic templates to specialist software, depending on organisational size and complexity.
You really can create a ‘glorified’ spreadsheet containing:
- Vulnerability or risk description: what’s the issue?
- System or asset affected: where does it live?
- Business impact: what happens if this goes wrong?
- Data impact: does it touch personal data, regulated data, or anything sensitive?
- Remediation plan: what are we going to do about it?
- Estimated cost and effort: people, time, money
- Target timeframe: now, next quarter, next budget cycle
- Owner: who is responsible for moving this along?
- Status and updates: what’s been done so far?

Please feel free to get in touch with us and we can send you some more examples of this.
If a meeting concludes with, “We’re not spending the money now, but we are committing to fund this in the next budget cycle and accept the risk in the meantime,” that decision should be traceable back to an entry in that register.
For IT managers, IT directors, heads of IT or cyber security professionals, this is a big part of “doing your job effectively”. You’ll be presenting risk clearly, in a way that fits how the organisation actually runs.
Where MSPs & SMBs Fit Into This
For MSPs, this framework is especially powerful. Clients often assume cyber governance is happening somewhere in the background, when in reality, many SMBs have never formally logged risk at board level. They may have vulnerability scans, and they may have patching policies, but they lack a governance trail.
Helping clients implement structured risk logging elevates your role, moving you from technical support to a governance partner. And from a defensive perspective, you protect yourself. If a client later faces an incident, you can demonstrate that risk was identified and escalated appropriately.
The Bigger Picture: Being a “Good Citizen”
Terry references working with global investment banks and large enterprises. The consistent theme across those environments is evidence.
If you can demonstrate:
- Ongoing vulnerability assessment
- Clear prioritisation
- Budget-aligned remediation plans
- Board-level visibility
... then you are operating as a responsible organisation.
This is what regulators look for, customers increasingly expect, and investors want reassurance around.
If you’d like examples of how to structure that or want to talk through how this applies to your MSP or organisation, please reach out to us via email: hello@roboshadow.com . We’re always happy to walk through the scenarios in more detail.
Another reminder that RoboShadow provides a structured, continuous view of your external attack surface and vulnerabilities. We identify issues, categorise them, and help translate technical findings into something that can be understood at a business level. Rather than relying on ad-hoc scans, fragmented reports, or technical findings that never quite make it to the board pack, RoboShadow aims to make operations smoother and more comprehensive at the same time.
Thank you for your ongoing support and feedback, and if you have any questions, please don’t hesitate to reach out to us at hello@roboshadow.com
.png?width=516&height=328&name=Add%20a%20heading%20(23).png)
Sources:
The insights above are based on a YouTube video by Terry Lewis, CEO of RoboShadow, as well as:
Cyber security breaches survey 2025 - GOV.UK
ISO/IEC 27001:2022 - Information security management systems
Capita fined £14m for data breach affecting over 6m people | ICO
2025-dbir-executive-summary.pdf
How do we document our processing activities? | ICO




