Patch Tuesday: April 2026
April showers bring May flowers, and this month Microsoft patched 167 vulnerabilities, including two publicly disclosed zero-day issues and eight critical vulnerabilities.
This blog breaks down the critical vulnerabilities that need to be addressed with this month's patch.
You can find Microsoft’s full April 2026 security update notes here.
Key Updates
-
167 vulnerabilities patched
-
2 publicly disclosed zero-day vulnerabilities
-
8 critical vulnerabilities
What is a Zero-Day vulnerability?
A zero-day vulnerability is a security flaw that becomes known to attackers before defenders have had a fair chance to patch it. In practice, that means there are effectively zero days of warning once details are public or exploitation begins. Even where exploitation has not yet been confirmed, a publicly disclosed flaw usually raises the urgency because attackers now know exactly what to start testing against exposed systems.
Vulnerability Types Released in April 2026
Elevation of Privilege once again dominates this month’s release by a significant margin, continuing a trend we’ve seen throughout 2026 so far. Remote Code Execution and Information Disclosure follow behind, but at a much lower volume.
Zero-Day Vulnerabilities
CVE-2026-33825: Microsoft Defender Elevation of Privilege Vulnerability
-
Description: This publicly disclosed zero-day affects Microsoft Defender and allows an attacker to elevate privileges locally due to insufficient access control.
-
Impact: As Defender sits at the core of endpoint protection, privilege escalation here is particularly sensitive. If exploited as part of a wider attack chain, it could allow an attacker to gain higher-level access on a system and potentially interfere with security controls or maintain persistence.
-
Remediation: Ensure Defender updates are applied across all endpoints and verify that systems are receiving the latest security intelligence and platform updates.
CVE-2026-32201: Microsoft SharePoint Server Spoofing Vulnerability
-
Description: This actively exploited zero-day affects Microsoft SharePoint Server and is caused by improper input validation. It allows an unauthenticated attacker to perform spoofing over the network.
-
Impact: Although this is not a remote code execution vulnerability, it still carries real risk. Exploitation could allow attackers to manipulate how SharePoint content is presented or accessed, potentially exposing sensitive data or supporting further attack stages. Given how widely SharePoint is used for internal collaboration and document management, this becomes particularly relevant in enterprise environments.
-
Remediation: Patch all SharePoint Server instances immediately, especially those exposed externally or used across multiple teams. This should be treated as a priority due to confirmed in-the-wild exploitation.
Critical Vulnerability Summary
Here are the critical CVEs from this month’s release:
| Product / Component | CVE | Title | Severity |
|---|---|---|---|
| .NET Framework | CVE-2026-23666 | .NET Framework Denial of Service Vulnerability | Critical |
| Microsoft Office | CVE-2026-32190 | Microsoft Office Remote Code Execution Vulnerability | Critical |
| Microsoft Office Word | CVE-2026-33115 | Microsoft Word Remote Code Execution Vulnerability | Critical |
| Microsoft Office Word | CVE-2026-33114 | Microsoft Word Remote Code Execution Vulnerability | Critical |
| Remote Desktop Client | CVE-2026-32157 | Remote Desktop Client Remote Code Execution Vulnerability | Critical |
| Windows Active Directory | Windows Active Directory Remote Code Execution Vulnerability | Critical | |
| Windows IKE Extension | CVE-2026-33824 | Windows Internet Key Exchange (IKE) Service Extensions Remote Code Execution Vulnerability | Critical |
| Windows TCP/IP | CVE-2026-33827 |
Windows TCP/IP Remote Code Execution Vulnerability | Critical |
Actions to Take
-
Patch SharePoint immediately
CVE-2026-32201 should be treated as a priority, particularly for any internet-facing or heavily used SharePoint environments. -
Ensure Defender updates are fully applied
Verify that all endpoints are receiving the latest Defender platform and security intelligence updates. This is not one to assume is covered. -
Move quickly on Office and endpoint updates
The number of Office and Word vulnerabilities this month reinforces the need to prioritise user endpoints, especially for teams regularly handling external documents. -
Prioritise core infrastructure systems
Active Directory, RDP, TCP/IP, and IKE-related vulnerabilities should be addressed early, particularly where systems are exposed or form part of critical internal services. -
Keep an eye on privilege escalation risk
With elevation of privilege continuing to dominate, it’s worth reviewing how easily an attacker could move from initial access to full control within your environment.
To Conclude
April’s Patch Tuesday is a larger release, but the pattern hasn’t really changed. There's a steady stream of privilege escalation vulnerabilities again, alongside a handful of critical remote code execution issues across Office and core Windows services.
The zero-days will naturally get most of the attention, especially with SharePoint already being exploited, but it still comes down to understanding what's affecting your environment and what needs prioritising.
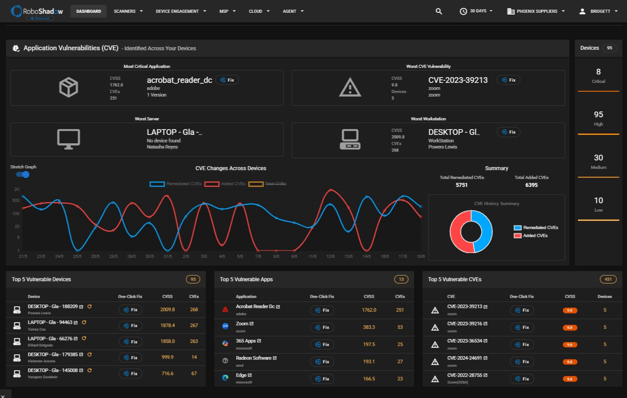
We understand how tricky this can be, as assets sit across different environments and patching priorities can become unclear when volume increases. RoboShadow helps simplify this by continuously mapping your external attack surface, giving you a clearer view of what’s exposed, which vulnerabilities are relevant, and where patching should be focused first. Especially in months like this, having that visibility makes prioritisation far more manageable.
As always, thank you for your continuous support and feedback, and if you have any questions, please don’t hesitate to reach out to us at hello@roboshadow.com



